|
The Matrix v0.5.2
| |
| |
| |
Summary
|
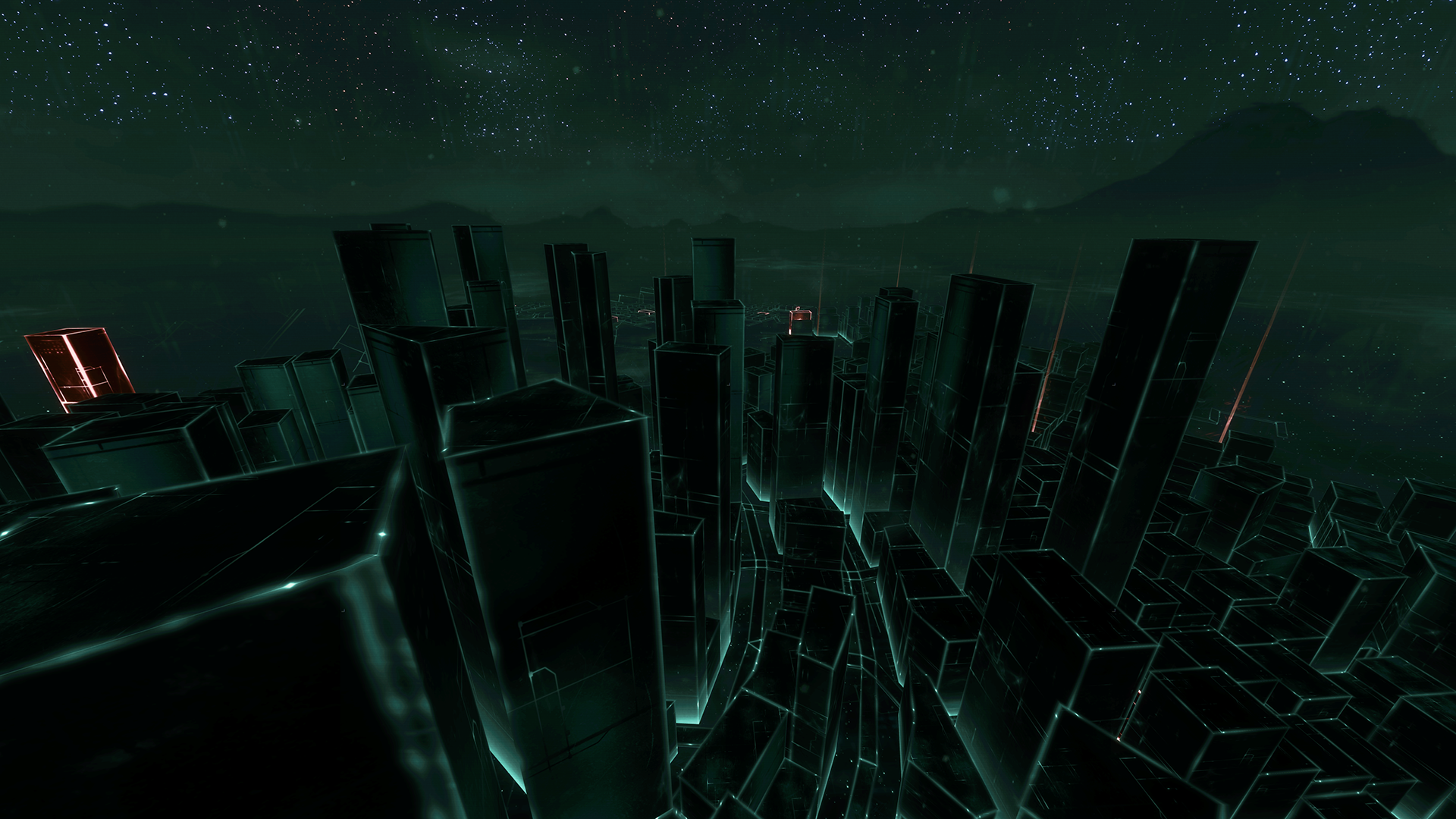
On February 17th, 2021, a psychic pulse was felt all over the globe. It began somewhere in Haven and radiated out. This was the birth of the Matrix, but not the virtual reality simulation that so many had envisioned. Instead, it was a dreamworld constructed around a new iteration of the various world wide networks and systems, combined, accessed through technology to bridge the gap of the subconscious mind through the Nightmare.
This new construct blends some stylistic interpretations of some popular culture and science-fiction themes, but is overlayed atop the real world, in real time, using realistic virtual imagery to represent the current network and information structures of the world. Most people in the world drift in as Guests and Users, drifting along data streams with simple interfaces. Other power users can attack these systems and circumvent the security measures, while others work to build said security measures.
The blending of reality with this construct allows for certain aspects of a dreamer to be manifested, restricting access to certain abilities in the Matrix. Non-Electropathic dreamers are limited to 'electronic access' via their computer hardware, called a Commlink, using programs. Electropathic dreamers skip the hardware and access these data streams directly with their minds.
This dreamworld is alive and evolving. It is being constantly monitored by the main Architect, KaOS.
|
|
| |
Special Notes
- Most Non-Electropathic Dreamers will appear as their normal self. Residual Self Image is a fact. As part of this, all Dreamers are not aware that this is a dream. They believe this is a real, technological Virtual Reality Construct. As such, Dreamers also remember and believe they are their real self.
- Trust is available for certain Roles, noted in those descriptions, pending approval.
- Petitions can be used by certain roles to add and modify this world's map, as noted in their descriptions.
- Movement through the Matrix is not unrestricted. Secured pathways will have descriptions that denote any required statistics to get past them. Please do not go into areas you should not be able to access.
- This world references works like The Matrix Movies, Shadowrun, and Ready Player One for much of its aesthetic.
- An item can be used by non-aware, non-electropathic, or mundane sorts to reach this world. This item is available at Flo-Tronics, in Haven, and it is called: a black, helmet-like, visored, L-666 model VR headset. Instructions for how to reach the Matrix Dreamworld are available as part of the item's description.
|
|
| |
Glossary
|
| |
History
- Launch Day Event, Log Coming Soon?
- Patch complete. Matrix v.0.6.4 now online. Patch notes: Haven Courier System attached to Historic District Grid. The Hive System attached to the Urban District Grid. The Network 666 System attached to the Redlight District Grid. Most parameters are acting as expected. Gravity optional settings functioning. Vehicular physics functioning within established models. Fixed an issue with connection to the Global Grid, should function properly now. Please petition with any connectivity issues. Cheers! - KaOS
- Small update, patching to Matrix v0.7.0. Blackfield System is half in. A barrier has been put up around Global Grid, preventing entry until the Moon Node is found, explored, and secured. Three people have died from visiting it. Caution highly recommended. Next update should finish Blackfield and expand the Beach area in the Tourist District node! Later. - KaOS
|
|
| |
Roles
- Guest
Some people are not quite ready to adopt the Matrix full time, so they have not actually registered any kind of account. The have just enough privileges for logging in, looking around, and probably managing to get into more trouble than anything else. Uses a commlink for access.
- User
A registered Matrix user, with all of the pros and cons that that entails. Realistically not a lot different than a Guest, but they can actually have access privileges and store intel/data for later. Uses a commlink for access.
- Hacker
Can alter their Avatar within realistic humanoid shapes/color ranges.
Some Matrix denizens are neither neither Guests not Users, but they still manage to get around and into trouble by sliding past security. Using advance programs on their commlinks, hackers live for the challenge of well designed systems, stealing whatever intel they can manage from them.
- Security
Can be assigned as Security to a System.
Security personnel are the main intelligent defense against hackers and those with malicious intent. While in their assigned System, Security can Emit actions of the System's defensive programs in conjunction with their own activities. Uses a commlink.
- Technomancer
Requires the dreamer to have Electropathic stat trained.
Can Petition for Trust.
Can alter their Avatar within realistic humanoid shapes/color ranges.
Blessed with not needing a commlink, technomancers manipulate data streams directly with sheer force of will and the power of their mind. While this is a taxing endeavor, they can get past security and firewalls even good hackers would have trouble with. Uses various mental katas known as Forms.
- Administrator
Can Petition for Trust and a System (rooms) to claim and Administrate.
A System Administrator is able to use far more of a System's resources in defense of the System than regular Security Personnel. Where Security can Emit for the System's defenses, the Administrator IS the System's defenses in a very direct sense, dispatching the ICe and cleaning up any malicious code. Uses commlink.
- Daemon
Requires the dreamer to have Electropathic stat trained.
Requires Demonborn, Demonic Pact Holder modifier, or Pact relationship with a Demon.
Can Petition for Trust.
Can alter their Avatar into any shape/design desired.
Daemons are the most terrifying presence on the Matrix. They are juggernaughts of destruction and even the coordinated efforts of several Security personnel are rarely enough to stop them from smashing through the defenses of a System. Daemon use rage and savagery to fuel their Forms.
- Architect
Can Petition for Trust and a System (rooms) to claim and Architect/Administrate.
Architects 'own' Systems on the Matrix. They choose the decor, they assign personnel, they manage access levels and privileges. They construct the themes and the aesthetics.
|
|
| |
Stats
- Hacking
This stat caps at the dreamer's real Hacking stat.
O: 1, D: 1
Available to Roles: All.
Hacking is used to access areas with restricted access by means of subverting security systems.
- Engineering
This stat caps at the dreamer's real Engineering stat.
O: 1, D: 1
Available to Roles: All.
Engineering represents knowledge of computers, commlinks, and most things mechanical and electrical.
- Knowledge
This stat caps at your the dreamer's real Occult Knowledge or Education stat (whichever is higher).
O: 1, D: 1
Available to Roles: All.
Knowledge is the sum of a person's acquired book knowledge, though which kinds of books is largely irrelevant.
- Privileges
O: 2, D: 0
Available to Roles: All but Guest.
Privileges represent legitimate, often paid, access to certain systems. Essentially accounts and passwords to get through the correct channels.
- Intel
O: 0, D: 2
Available to Roles: All but Guest.
The entire purpose of the Matrix is to disseminate knowledge and information, and those with Intel to share are often well regarded.
- Exploit
O: 3, D: 0
Available to Roles: All but Guest and User.
Program. Most hackers live or die by their exploit program, using it to slice through vulnerabilities to gain access to a system or penetrate an ICe's defenses to shut it off.
- Stealth
O: 1, D: 2
Available to Roles: All but Guest and User.
Program. Avoiding detection is usually the best line of defense for hacker sorts, and the evasion program assists in positioning and blending in with the background data to avoid being seen. Also assists in setting up ambushes against the unwary.
- Armor
O: 0, D: 3
Available to Roles: All but Guest and User.
Program. A hacker will eventually be found, detected, and likely come under direct, if electronic, assault. The armor program helps them avoid getting scorched when the IC tries to tear into their brains.
- Agent
O: 2, D: 1
Available to Roles: Hacker.
Program. A minor digital assistant AI that can do some activities with semi-autonomy, depending on the complexity of the directions.
- Spider
O: 1, D: 2
Available to Roles: Security.
Program. A minor digital assitant AI that can do some activities with semi-autonomy, depending on the complexity of the directions.
- Sprite
O: 2, D: 2
Available to Roles: Technomancer.
Sprite. Technomancer version of an Agent that is far more capable and intelligent than the mundane counter part.
- Evasion
O: 1, D: 3
Available to Roles: Technomancer.
Form. Technomancer version of a Stealth program, but focused more on speed and blurring their avatar to keep from being detected or hit.
- Warfare
O: 3, D: 1
Available to Roles: Technomancer.
Form. Technomancers engage in cybercombat a little differently, through Electronic Warfare, signal jamming/disruption, static/noise, and focused bursts.
- Sprite
O: 2, D: 2
Available to Roles: Technomancer.
Sprite. Technomancer version of an Agent that is far more capable and intelligent than the mundane counter part.
- Vaccine
O: 0, D: 4
Available to Roles: Administrator.
Program. The pinnacle of anti-virus software, the Vaccine has been known to scorch viruses even before they are deployed by building up libraries of malicious code to innocuate a system before hand.
- ICe
O: 3, D: 1
Available to Roles: Administrator.
Program. Intrusion Countermeasures, system-side programs that constitute the defense of that network and its resources. Some versions can actually be lethal to the meat body of their targets.
- Blackhammer
O: 5, D: 1
Available to Roles: Daemon.
Form. Advanced Daemon ability, creates a weapon (of any kind) that is edged with lethal, Black-ICe protocols for cybercombat against human opponents. Can also be used to smash ICe, but the lethal subroutines are less efficient in this.
- Firewall
O: 1, D: 5
Available to Roles: Daemon.
Form. Advanced Daemon ability, creates an electronic wall of fire to burn away and purge all malicious code being directed toward the one using the ability. Has been known to scorch nearby connections as well.
- Cybercombat
O: 3, D: 3
Available to Roles: Daemon.
Form. Advanced Daemon ability, essentially blending electronic warfare and speed into a devastating but still sustainable flurry akin to martial arts mastery.
- Revoke
O: 5, D: 0
Available to Roles: Architect.
Program. A program designed to nullify an avatar's access privileges and render all nearby security systems on high alert against the avatar. Particularly devastating on systems that utilize lethal Black ICe defenses.
- Quarantine
O: 0, D: 5
Available to Roles: Architect.
Program. Next generation Vaccine software that safely sequesters incoming malicious code before it can even get close enough to be a threat to the system.
|
|
| |
RP Guide
|
| |
Systems Within the Matrix
|
Systems are an integral part of what will make the Matrix function for Dreamers in the intended fashion of the Demon that created the system. As a reminder, no Dreamer should ever take an exit with access requirements that they do not meet. The only exception is people that have been dream invaded/snared or recovered from dream attacks; they can depart a system without worry.
- What is a System?
Most Systems are a set of 1-3 rooms, designed by an Architect. Each room can have different access requirements. Often these systems will have a Public 'front' room that allows traffic in from the Matrix. From there, sub systems usually have more restricted access.
Example: The Network 666 System is integrated into the Haven LTG and chat servers. It does not have a strictly public 'front room,' as only someone with a bit of skill can access it. But once inside, the lounge area is meant to be a semi-public space to talk about various supernatural topics.
- What does a System look like?
The Architect that 'owns' a system determines this. The outward appearance can be generalized for public view, but inside, the environment can be sculpted into any fashion the Architect pleases. The iconography of the Matrix is semi-real, semi-tangible, and all five senses can be indulged through the VR Construct. That means a bakery system could have the smell of fresh baked cookies or pies within it. A concert hall could have orchestral music playing. All of these details are selected by the Architect.
- How do I get a System?
Getting a system can be done one of two ways. The easiest way is with an OOC Note to Lilith, requesting the System be setup. Alternatively, a Petition in the dreamworld can be used for anonymity's sake. Please provide names for the rooms and descriptions. If color codes are important and extensive, please feel free to use a PasteBin Link for them. Additionally, a room may have Six Access Points, split between the Five Access Stats (Hacking, Engineering, Knowledge, Privileges, and Intel). These access points work like Stats in Haven, 1 point for 1, 3 points for 2, 6 points for 3.
Example: The Network 666 System requires Hacking 2 and Knowledge 2, each of which cost 3 Access Points, for a total of 6. That is to get into the front door, the main chat/lounge area, essentially. But there is a Paid Access area that requires Privileges 2 and Intel 2. You have to pay to get in and share information within the paid area. A second area called the Void branches off from the Lounge as well, but it requires Hacking 3 to get in.
- Why do I want a System?
Aesthetics aside, there are benefits to having a System. The first is, a place with relative control over who can get in, limiting access. This allows for a semi-private area of the Matrix where the Architect and their team can congregate, plan, scheme, or socialize. It also gives options for certain nefarious sorts to hide victims they have brought in for interrogations or interviews. The people that would normally come to rescue these victims will be stymied by the System's defenses.
Example: A Hand member has dream invaded a local Templar into the Matrix for an interview. The Hand Member drags the Templar into Network 666, because they have Hacking 3 and Knowledge 2. The Hand member then continues past the Lounge and into the Void. Temple operatives hear of the assault, and they go in to try to rescue the intial Templar. But none of them have Hacking 3. Though they can get in the front door of the Lounge for Network 666, they cannot get through and into the Void. The Network 666 system defenses prevent it, letting the Hand member finish their work and drop the Templar off in the Lounge.
- How do I improve a System?
Maintaining and improving a system is not a solitary task. An Architect can build a bunch of Systems, but they will all be relatively easy to plunder and poke at, with a bare minimum of access requirements. To add additional Access Points to their system, they need additional personnel. A System gains an Access Point for every Security person that assigns themselves to the System. A System gains an additional two Access Points for every Administrator that assigns themselves to the System. These points are for the System and can be assigned to a specific Room of the System. To assign themselves as to a System, Security and Administrators need an appropriate Fame line and a Petition for where they want their Access Points utilized in the System. If they later change Systems, these points will be removed.
Example: Jim is a Security sort, but he does not have a friend that is an Architect. Instead, he wants to assign himself to the Network 666 System and assist with their Security. He sets his Fame to something about being known for taking extra measures to secure the Void on Network 666. He petitions and asks to be assigned to Network 666 with his Access Point being for the Void, requiring some degree of Engineering as well. The Void's new Access Requirements are now Hacking 3, Engineering 1, until Jim leaves Network 666.
- Can two Architects combine their rooms/Access Points?
Yes, however. After the first Architect in a System, each additional Architect only provides 1 additional 'room' to the System. This room has the standard 6 Access Points. For having additional Architects, the System gets 3 extra Access Points, used exactly the same as Security/Administrator's extra points. However, because of the way Architects build these Systems, they are non-transferrable. If that Architect later wants to leave that System, their points stay behind. They can however build a new System with the standard Access Points. They cannot ever assign additional points to a third System.
Example: Mary comes along, and she is an Architect. She likes Jim as a security sort, so she decides to join him in improving Network 666 instead of making her own System. She decides the Network 666 network is mostly fine, but it needs a really deep, dark bottom of the Void. Using her 3 Access points and the standard 6 Access Points for the room, she creates the Singularity off the Void room. This is the vault of all the forbidden knowledge the Network has gathered over the years, and she wants a pretty major lock on it. She has Jim reassign his point from Engineering 1 in the Void to her new room, for a total of 10 access points, then slams the door to it closed for anyone that does not have Knowledge 4 to unlock the arcane puzzle lock on it. The Void's access requirements return to Hacking 3, but only the truly studious will be worthy of the secrets in the Singularity Vault. If Mary decides to leave Network 666 to make her own System, she can, but she can never join another System to give it extra Access Points for an extra Architect.
|
|
| |
Roster
|
|
|